Mm iso 27001 2013 +annex a
•
0 likes•2,389 views
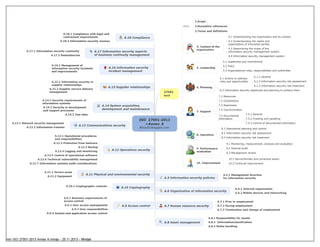
майндкарта по ISO 27001-2013
Report
Share
Report
Share
Download to read offline
Recommended
пр Разработка комплекта документов по управлению ИБ (прозоров)

пр Разработка комплекта документов по управлению ИБ (прозоров)Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
More Related Content
What's hot
What's hot (20)
Iso iec 27001 foundation training course by interprom

Iso iec 27001 foundation training course by interprom
My Gap analysis results between ISO27001: 2022 and 2013 version as of 2022 fall.

My Gap analysis results between ISO27001: 2022 and 2013 version as of 2022 fall.
ISO 27001 Certification - The Benefits and Challenges

ISO 27001 Certification - The Benefits and Challenges
Iso iec 27032 foundation - cybersecurity training course

Iso iec 27032 foundation - cybersecurity training course
Viewers also liked
пр Разработка комплекта документов по управлению ИБ (прозоров)

пр Разработка комплекта документов по управлению ИБ (прозоров)Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
пр 01.актуальный ландшафт угроз иб (jsoc нн) 2015 08-21

пр 01.актуальный ландшафт угроз иб (jsoc нн) 2015 08-21Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
пр Принцип 80 на 20 для обеспечения кибербезопасности 

пр Принцип 80 на 20 для обеспечения кибербезопасности Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
Viewers also liked (20)
пр Разработка комплекта документов по управлению ИБ (прозоров)

пр Разработка комплекта документов по управлению ИБ (прозоров)
пр 01.актуальный ландшафт угроз иб (jsoc нн) 2015 08-21

пр 01.актуальный ландшафт угроз иб (jsoc нн) 2015 08-21
How to better understand the context and the scope of the BCMS?

How to better understand the context and the scope of the BCMS?
пр Принцип 80 на 20 для обеспечения кибербезопасности 

пр Принцип 80 на 20 для обеспечения кибербезопасности
Similar to Mm iso 27001 2013 +annex a
ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Poster

ISO/IEC 27001:2022 (Information Security Management Systems) Awareness PosterOperational Excellence Consulting
Similar to Mm iso 27001 2013 +annex a (20)
Iso 45001 guia comparacion ohsas 18001 -iso-dis 45001

Iso 45001 guia comparacion ohsas 18001 -iso-dis 45001
ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Poster

ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Poster
PECB Webinar: Risk-management in IT intensive SMEs

PECB Webinar: Risk-management in IT intensive SMEs
Information Security Management Systems(ISMS) By Dr Wafula

Information Security Management Systems(ISMS) By Dr Wafula
ISO 45001 – Health & Safety International Standard

ISO 45001 – Health & Safety International Standard
More from Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
NIST Cybersecurity Framework (CSF) 2.0: What has changed?

NIST Cybersecurity Framework (CSF) 2.0: What has changed?Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
My 15 Years of Experience in Using Mind Maps for Business and Personal Purposes

My 15 Years of Experience in Using Mind Maps for Business and Personal PurposesAndrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
ISO 27001 How to use the ISMS Implementation Toolkit.pdf

ISO 27001 How to use the ISMS Implementation Toolkit.pdfAndrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001
More from Andrey Prozorov, CISM, CIPP/E, CDPSE. LA 27001 (20)
NIST Cybersecurity Framework (CSF) 2.0: What has changed?

NIST Cybersecurity Framework (CSF) 2.0: What has changed?
My 15 Years of Experience in Using Mind Maps for Business and Personal Purposes

My 15 Years of Experience in Using Mind Maps for Business and Personal Purposes
ISO 27001 How to use the ISMS Implementation Toolkit.pdf

ISO 27001 How to use the ISMS Implementation Toolkit.pdf
ISO 27001 How to accelerate the implementation.pdf

ISO 27001 How to accelerate the implementation.pdf
All about a DPIA by Andrey Prozorov 2.0, 220518.pdf

All about a DPIA by Andrey Prozorov 2.0, 220518.pdf
Mm iso 27001 2013 +annex a
- 1. intro 4.1 Understanding the organization and its context 4.2 Understanding the needs and expectations of interested parties 4.3 Determining the scope of the information security management system 4.4 Information security management system 5.1 Leadership and commitment 5.2 Policy 5.3 Organizational roles, responsibilities and authorities 6.1 Actions to address risks and opportunities 6.1.1 General 6.1.2 Information security risk assessment 6.1.3 Information security risk treatment 6.2 Information security objectives and planning to achieve them 7.1 Resources 7.2 Competence 7.3 Awareness 7.4 Communication 7.5 Documented information 7.5.1 General 7.5.2 Creating and updating 7.5.3 Control of documented information 8.1 Operational planning and control 8.2 Information security risk assessment 8.3 Information security risk treatment 9.1 Monitoring, measurement, analysis and evaluation 9.2 Internal audit 9.3 Management review 10.1 Nonconformity and corrective action 10.2 Continual improvement
