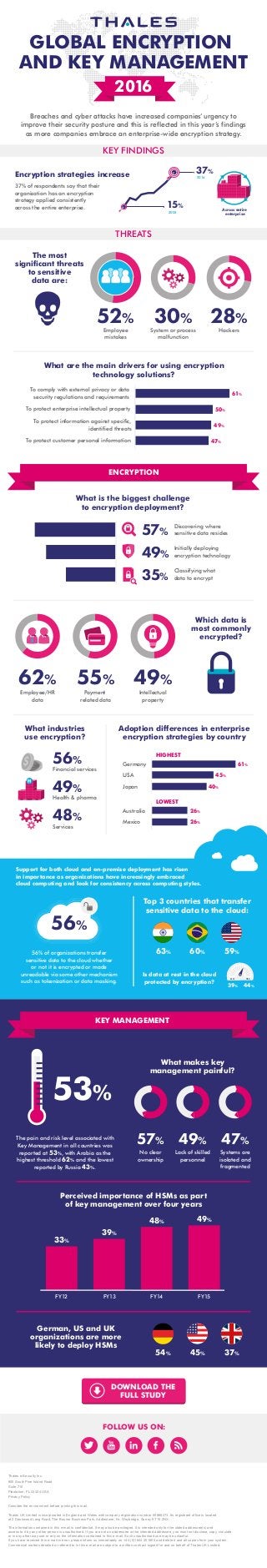
Global Encryption Trends Study 2016 Infographic
- 1. GLOBAL ENCRYPTION AND KEY MANAGEMENT 2016 Breaches and cyber attacks have increased companies’urgency to improve their security posture and this is reflected in this year’s findings as more companies embrace an enterprise-wide encryption strategy. KEY FINDINGS THREATS Encryption strategies increase 37% of respondents say that their organization has an encryption strategy applied consistently across the entire enterprise. Discovering where sensitive data resides Initially deploying encryption technology Classifying what data to encrypt Germany USA Japan HIGHEST LOWEST Australia Mexico 26% 26% System or process malfunction The most significant threats to sensitive data are: Which data is most commonly encrypted? What are the main drivers for using encryption technology solutions? 37% 57% 49% 35% 30% 55% Payment related data Financial services 56% Health & pharma 49% Services 48% 2016 15% Across entire enterprise2005 ENCRYPTION What industries use encryption? Adoption differences in enterprise encryption strategies by country 61% 45% 40% Support for both cloud and on-premise deployment has risen in importance as organizations have increasingly embraced cloud computing and look for consistency across computing styles. 56% of organizations transfer sensitive data to the cloud whether or not it is encrypted or made unreadable via some other mechanism such as tokenization or data masking. Is data at rest in the cloud protected by encryption? 56% Top 3 countries that transfer sensitive data to the cloud: 39% 44% NO YES KEY MANAGEMENT FOLLOW US ON: German, US and UK organizations are more likely to deploy HSMs Perceived importance of HSMs as part of key management over four years The pain and risk level associated with Key Management in all countries was reported at 53%, with Arabia as the highest threshold 62% and the lowest reported by Russia 43%. 53% No clear ownership Lack of skilled personnel Systems are isolated and fragmented What makes key management painful? 57% 49% 47% 54% 45% 37% 63% 60% 59% Thales e-Security Inc. 900 South Pine Island Road Suite 710 Plantation, FL 33324 USA Privacy Policy Consider the environment before printing this mail. Thales UK Limited is incorporated in England and Wales with company registration number 00868273. Its registered office is located at 2 Dashwood Lang Road, The Bourne Business Park, Addlestone, Nr. Weybridge, Surrey KT15 2NX. The information contained in this e-mail is confidential. It may also be privileged. It is intended only for the stated addressee(s) and access to it by any other person is unauthorised. If you are not an addressee or the intended addressee, you must not disclose, copy, circulate or in any other way use or rely on the information contained in this e-mail. Such unauthorised use may be unlawful. If you have received this e-mail in error, please inform us immediately on +44 (0)1844 201800 and delete it and all copies from your system. Commercial matters detailed or referred to in this e-mail are subject to a written contract signed for and on behalf of Thales UK Limited. Hackers 28% Employee mistakes 52% 49% Intellectual property 62% Employee/HR data DOWNLOAD THE FULL STUDY To comply with external privacy or data security regulations and requirements To protect information against specific, identified threats To protect enterprise intellectual property To protect customer personal information 61% 50% 49% 47% FY12 FY13 FY14 FY15 33% 39% 48% 49% What is the biggest challenge to encryption deployment?
