Sponsors Deserve Trustworth Electronic Patient Reported Outcomes (ePROs)
- 1. 1 PHT Insights — Second Quarter 2009 Sponsors Deserve Trustworthy Patient Reported Outcomes How PHT Safeguards Electronic Patient Reported Outcome (ePRO) Data Collected from Global Clinical Trials Sponsors and CROs must be assured that Since PHT collects and produces electronic records that become part of a submission to clinical data collected for regulatory submis- global regulatory agencies, data on these electronic diaries (eDiaries) must be of high sions comply with the regulations and guidance integrity and quality, and trustworthy sources of scientific findings. The PHT Quality around the world for data quality and integrity. Management System (QMS) has been designed with safeguards that reach beyond government requirements for safe data, secure data, archived and easily retrievable Regulatory agencies are placing more emphasis data. PHT is the only ePRO handheld eDiary provider with ISO 9001:2000 certification on the voice of the patient, and they are auditing of its Quality Management System – one of the reasons why most of the world’s largest patient reported data for validity and trust- pharmas choose PHT to collect ePRO data for their global studies. worthiness. Intuitively, capturing patient data electronically instead of on paper would seem T To ensure that best practices are capable of providing valid data more reliably Benefits of ISO 9001:2000 Certification leveraged with each trial, PHT and efficiently. PHT has demonstrated that provides scientific and technical • Superior Product Quality review throughout the sales and this is true. • More Reliable Technology project development stages to All PHT products meet the requirements of the help clients specify ePRO data United States Food and Drug Administration • Efficient Business Processes, Saving Time g gathering requirements for (FDA), the European Medicines Agency (EMEA), and Money e each clinical trial. Once these the European Union (EU), the International • Global and Repeatable Quality Standards d data requirements have been Conference on Harmonisation of Technical c confirmed for a trial, PHT builds Requirements for Registration of Pharmaceuti- • Continual Improvement of Processes a and tests a prototype that is s shared with the client, and (1) cals for Human Use (ICH), the Pharmaceuticals makes changes to the ePRO and Medical Devices Agency in Japan (PMDA), s system based on review of the and others. These regulations and guidelines prototype with th client, (2) translates diary screens with validated translation text, t t ith the li t t l t di are intended to ensure that the electronic systems (3) performs full validation and supports User Site Testing (UST) of the system with the used in clinical research are safe and protected client, and (4) trains both sponsor and site personnel. from tampering; that the electronic records such as ePRO diaries are accurate, reliable, and PHT has four phases of internal processes and procedures that ensure that all eDiary auditable; and that personal information of trial data are of the highest quality – whether collected by a mobile PDA for home entries, or a touch-screen tablet PC for office entries. subjects is protected. This document describes how PHT provides data security through its software applications, data transmissions, physical data storage, database 1. PHT Electronic Mobile Devices are Configured to Collect and documentation backups, and audit trails. Clean Data. To ensure that high quality data are captured on every eDiary, all PHT devices are designed to verify date and time of data capture, and apply edit checks and logical Contents branching. Once each eDiary is designed, PHT conducts extensive internal testing of 1. Configuration of each eDiary System p.1 each application, and documents conformance to the protocol requirements for data capture. Internal tests of each device and ongoing calibrations during trial execution 2. Pre-Deployment Testing of Mobile Devices p.3 prevent discrepancies such as conflicting time stamps per diary, incomplete diaries or diaries that are out of sequence, or loss of data during transmissions regardless of line 3. Execution of Data Collection and Storage p.3 or signal quality. There are several product capabilities and PHT practices that enable 4. Real-Time Data Review and Archive p.4 all study configurations to reach a high standard of data quality and integrity:
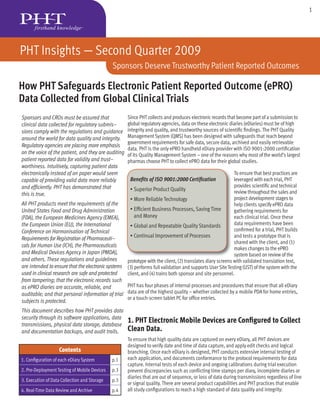
- 2. 2 PHT Insights – Second Quarter 2009 Sponsors Deserve Trustworthy Patient Reported Outcomes Data entered are time- When a PHT mobile stamped accurately. 5 Steps to Submissible Data device battery has run PHT synchronizes study 1. 2. 3. 4. 5. low, the internal logic server clocks hourly with PHT Scientific & ePRO Data ePRO Data Sites & Sponsors Archive of ensures that the device US National Institute of Technical Teams Collected Transmitted to Authorize Real-Time Complete and clock is synchronized Standards and Technol- Configure Mobile at Home or StudyWorks Access to Data Untampered XML in advance so that any Devices to Collect at Site and Redundant Record Available ogy (NIST) time serv- Clean Data Servers for Audit new data are accurate- ers, and monitors the ly time stamped. Authorized Queries performance of its clocks Time of data entry to ensure that time server can be scheduled. disparities from the Subjects using paper NIST atomic clock never diaries have long been exceed 1 second. All known to record data PHT ePRO mobile device in advance, or hours clocks, which keep UTC, or days after the time are monitored for accu- Complete Complete Backup Confirmed Transmissions required in the study racy and resynchronized Confirmed protocol schedule. at each transmission Retrospective reporting when they connect to the of symptom severity is server. Daylight savings of questionable value. Subjects may report past symptoms based on rules and time zone offsets are updated when governments change their current symptom experience. Using PHT ePRO provides certainty them. PHT tracks such changes world wide and updates the tables in that the report was done according to schedule. Such timely data have our devices so that they consistently show correct local time computed been reported to reveal efficacy of medications with smaller sample from an accurate UTC clock. sizes than comparable data using paper methods where completion Data are edit-checked. PHT can design ePRO questions to ensure that time was not enforced. subjects cannot leave any required question unanswered, or enter According to the FDA, “If a patient diary or some other data that violate logic. Examples of edit-checking include only allowing form of unsupervised data entry is used, the FDA plans to digits (and not text) in responses that must be numerical, preventing review the protocol to determine what measures are taken entry of inappropriate dates in the future, and only allowing entry of to ensure that patients make entries according to the study blood pressure readings within the range that the measuring instru- design and not, for example, just before a clinic visit when ment can read. their reports will be collected.” 1 Screens follow a logical branching sequence. In each eDiary, subjects are automatically directed to the next logical question in order Devices and data can drive required activities. PHT devices sup- to preclude entering inconsistent or conflicting data. Subject comments port pre-programmed or conditional alarms to remind the subject can be supported, but, unlike paper data methods where marginalia that it is time for data reporting or time to take medications or can be abundant, comments such as “my hair hurts” can be limited treatments. All entries made on PHT devices include a date and to particular screens for appropriate levels of review or simply time stamp to validate the timeliness of all captured data down to prevented. the minute. Additionally, the PHT system can be set up to generate automatic email alerts to sites and sponsors when subjects fail to Data entry is restricted to authorized users. Each PHT mobile device comply with the protocol, or when they report clinical conditions that features logical protection with a unique encrypted and hidden pass- merit site support. word for sharing information with the PHT database via StudyWorks . In ® addition, each device can support several levels of access controls cho- Data remain unchanged and protected from premature loss or sen and/or entered by the subject (or other authorized person) to whom destruction. Government regulations require that sites prepare and the particular device has been assigned. Access controls help ensure maintain source data. PHT enables site investigators to fulfill these that captured data are fully attributable. For maximum data security, all requirements by protecting all original eDiary data in StudyWorks exchanges of data during transmissions are encrypted and are compre- where authorized site personnel can access them at will, review hensively logged on both StudyWorks and the mobile device to preserve them or cause them to be corrected. Full audit trail records are the contextual information pertaining to each transmission. 1 Lines 334-337, ‘Guidance for Industry. Patient-Reported Outcome Measures: Use Data are protected during battery removal, low voltage and in Medical Product Development to Support Labeling Claims. DRAFT GUIDANCE.’ U.S. device resets. Device monitoring logic ensures that devices operate Department of Health and Human Services, Food and Drug Administration, Center for Drug properly throughout the trial and prevents the possible corruption of Evaluation and Research (CDER), Center for Biologics Evaluation and Research (CBER), results if batteries get too low or users trigger inappropriate resets. Center for Devices and Radiological Health (CDRH). February 2006.
- 3. 3 PHT Insights – Second Quarter 2009 Sponsors Deserve Trustworthy Patient Reported Outcomes automatically made of documents by the US any changes to the data Federal Drug Administra- after entry, including the tion on subject informed retention of the original consent and subject value, date/time stamp protection, Institutional of the change, the iden- Review Boards (IRBs), tity of the person who Investigational New made the change, and Drug (IND) devices, and the dated digital signa- adverse event reporting. ture for attribution. PHT has considered Data remain privacy protection a confidential. Personal design imperative for its Data Protection is a system. The mandates universal Human Right, of worldwide regulations as affirmed in the PHT presence are met and will continue Universal Declaration We’ll be to be met or exceeded of Human Rights – there soon by PHT’s Product Suite. Article 12, and the Unlike paper diary Convention for the collections, electronic Protection of Human PHT and ePro Around the World data capture increases Rights and Fundamental • 60% of all PHT trials are international subject safety with real- Freedoms – Article 8. • Language choices for subject and site – up to 16 on the same device time alerts for rescue Multiple global agencies • In-house production understands shipping and customs timelines medications and adverse and regulations events, and can do so protect the security without compromising and confidentiality privacy. of electronic health information, with the authority to enforce compliance with fines for breach, refusal to allow use of the data 2. PHT Electronic Mobile Devices Pass Strict collected, and/or legal consequences. PHT is in full compliance with regulations and guidelines for privacy of personal information for Internal Quality Testing Assurance Prior to study staff and subjects. Trial Deployment. The EU has created the broadest set of rules for protecting personal PHT conducts extensive internal validation testing of each device and data, based on OECD guidelines. The EU Directive requires that study design, to ensure conformance to the protocol requirements for data be (1) fairly and lawfully processed, (2) processed for limited data capture. To that end, the PHT study delivery function employs purposes, (3) adequate, relevant and not excessive, (4) accurate more testers than developers (currently a 3:1 ratio). and up-to-date, (5) not kept for longer than necessary, (6) processed As trial design engineers clarify protocol specifications for a specific in line with the rights of data subjects, (7) secure, and (8) not trial and begin writing code, the PHT Software Quality Engineering transferred to other countries without adequate protection. Many group develops appropriate test scripts. When completed, the test countries follow the lead of the EU Directive for personal health data scripts are reviewed against the client requirements to ensure all privacy. The United States seeks to protect data confidentiality at the required functionality is covered. Then they are used to test the study National level with specific data privacy rules in the US Health Insur- code and system operations to document that the system functions as intended. ance Portability and Accountability Act [HIPAA]; Japan’s Act of the Protection of Personal Information is based on the 8 OECD criteria. In addition to internal Quality Control (QC ) testing, user site testing The Asia-Pacific Economic Cooperation (APEC) 2005 framework is and database testing are undertaken for each trial. PHT project man- also based on the OECD guidelines, and is being further developed. agers work with clients to assure adequate time for user site testing. Turkey, Mexico, Israel, Dubai, China, India and Russia are preparing Sponsors who select vendors who do not conduct trial-specific internal data privacy laws. QC testing would be vulnerable under audit if asked to document that an ePRO system was known to function as intended. Subject or patient data are protected under The Declaration of Hel- sinki, as developed by the World Medical Association (WMA), the ICH 3. Standard Procedures Ensure Reliable Data Guidelines for Good Clinical Practice, the International Organization Collection, Transmission and Storage During for Standardization (ISO) Clinical Investigation of Medical Devices for a Trial. Human Subjects, the EU Good Clinical Practice Directive, and various
- 4. 4 PHT Insights – Second Quarter 2009 Sponsors Deserve Trustworthy Patient Reported Outcomes PHT strictly enforces its policies and procedures for sion break. If interrupted, data are secured on the secure data collection, communication and device and re-sent during a subsequent transmis- data storage. All mobile devices are tested sion. Further, all wireless and analog devices to ensure conformance to the protocol support automated retries and untended, scheduled requirements for data capture. transmissions. Collection of eDiary Data is Protected with The Physical Security of PHT Servers Ensures Safe Electronic Safeguards. Data Storage. PHT acknowledges that any technol- Sponsors must collect data that can be ogy leveraging mobile communications and the authenticated and attributable. For this Internet is subject to potential attacks and reason, each data entry response captured data tampering. As a result, PHT requires on a PHT device is linked by documented physical security provisions as part of its attribution steps to the particular subject security policy for the central electronic assigned the device and, if required, also to systems and servers used in all clinical the person who actually entered the report (a studies. proxy or an observer). PHT supports linking traditional handwritten signatures to ePRO All study servers are secured in a co- records and still preserves confidentiality. location facility as well as at a facility near or within the PHT offices. PHT Corporation Transmission of the eDiary Data to the selects its co-location facility based on PHT Server is Reliable and Redundant. Processes and methods ensure that data are documented physical security require- securely, accurately and dependably transmitted ments, and audits providers against those from the PHT mobile device to PHT StudyWorks. requirements. PHT also requires all key server functions to be redundant. Data are centralized and protected against tampering. Transmissions from PHT Corporation selects its Physical security measures: Servers are located the PHT mobile device to StudyWorks are co-location facility based on physical in locked facilities with environmental controls encrypted and contain session logs that and emergency power, and contained in locked are generated and monitored for all trans- security requirements, and ensures that cabinets within a caged area in the facilities. Sur- missions. All centralized data remains all key server functions are redundant. veillance cameras record activity throughout the both physically and logically secure. XML facility 24x7. Main access points have redundant source data are kept in encrypted packets so that any change (e.g. tampering via back-end access) will break security measures, with security personnel onsite 24x7 365 days a the encryption seal. PHT conducts regular tamper checks on all study year. Access to the servers is allowed for PHT authorized personnel data. It also performs back end checks for duplicate records or only, with each such access logged (name and time) in records kept inconsistent timestamps. for PHT to examine. Data storage is redundant. PHT executes “full” database backups After archiving, all retired data are destroyed. All PHT devices are de- daily, and keeps such backups securely offsite. Backups receive commissioned before they leave PHT, and contain no data. All hard the same logical security measures as the live databases on serv- disks are destroyed or wiped to ensure that no identifiable data are ers. Backup media are “tamper evident”, with encrypted backups retained. Certification of destruction is provided for all devices, ac- optionally supported. cording to the US Environmental Protection Agency (EPA) regulations, Data are monitored. All captured data are reviewable only by the and all known other local and national mandates. authorized StudyWorks users responsible for maintaining that data. Typical roles include site coordinators, study monitors, data manage- 4. Security Measures for Real-Time Data ment personnel and sponsor personnel, and each role has specific Access and Archiving. and different privileges for viewing or correcting data. During the web browser login to StudyWorks, users must present a login ID that PHT Only authorized personnel can access StudyWorks to view reports or validates to be different from all other users on all trials, and a hid- archival records. In addition, the StudyWorks server is dedicated ex- den “strong” password (not known to PHT) of at least 8 characters. clusively for acting on data captured by the PHT mobile device, and Sessions are encrypted under Secure Socket Layer (SSL) with 128 bit not used for any other purpose. Since StudyWorks is a web-based encryption. Each server has a public key for its SSL encryption that is solution, web authorization and control of passwords are critical. certified by a public company such as Verisign or Comodo. The PHT servers are certified and are capable of issuing client certificates Access to StudyWorks is protected by an administration module for SSL sessions. Accurate data summaries and/or electronic Case with authorizations and passwords. Only users having security Report Forms (eCRFs) for each captured report are viewable on Study- access to the Administrative Module for a study on the StudyWorks Works for investigators with valid accounts who properly execute the Server can set up access privileges to that study for other users. login procedure. Access to the Administrative Module is managed by authorized Data transmission interruptions are managed. Data transmission specialists at PHT whose performance is regularly reviewed by the procedures guard against data loss, even in the event of transmis- PHT Security officer. These PHT specialists obtain from sponsors the
- 5. 5 PHT Insights – Second Quarter 2009 Sponsors Deserve Trustworthy Patient Reported Outcomes names and identifying codes for each site investigator and other indi- viduals authorized to use the system for particular purposes (privileges) Sponsors Require in a deployed study. The StudyWorks application maintains an ongo- Trustworthy Patient ing log of all users and documents the history of authorization for all personnel, roles and privileges. Any signing of electronic records during Reported Outcomes the execution of a study is automatically included in the audit trail. An Electronic Signature Agreement (ESA) or other documented authoriza- PHT Safeguards ePRO Data tion traceable to the sponsor must be completed by all sponsor, site Collected from Clinical Trials and PHT personnel who will be accessing a PHT study using StudyWorks. ESAs are required for identity certification even for users who will simply PHT continues to lead the industry review data and who will not have editing privileges or the capacity to with data security measures for approve records. PHT LogPad® – The mobile PDA safeguarding electronic patient Personnel must be authorized. All individuals who have access to an reported outcomes. Data collected administrator account must have authorization that is documented and with PHT mobile devices are fairly and lawfully processed for recorded. These individuals agree in writing that they will not share their limited and defined purposes, with adequate, relevant, accurate, administrator password with any other person. Authorization is system- secure and validated capture. Data are not retained longer than atically and promptly revoked if an authorized person leaves PHT. A re- necessary. cord of each password account change, along with the time and purpose of the change, is kept in the System Administration Log. To date, PHT has collected data for more than 400 trials in 85 Password controls are required. To prevent any unauthorized access languages within 64 countries. NDA submissions based on PRO to StudyWorks, all user accounts for PHT computers must comply with data captured with the PHT system have resulted in many site the group security policy that is reviewed by the PHT Security Commit- inspections where PHT archival records have been relied upon tee. The PHT Information Technology (IT) Services group implements the and where sites and sponsors have thanked us for the detail, security policy provisions on the server at the direction of the Security unimpeachable quality, and ease of access to all the necessary Officer. Security configurations require system account passwords for records needed by regulatory authorities. server applications, differentiated active system account passwords, auditing for all logon events and actions, and a screen saver logon with PHT has exclusive worldwide rights to 8 patents related to its password protection. All consoles are physically locked and logically ePRO system. protected when not in use. The StudyWorks archive of all study source data is verified and stored PHT ePRO Data Integrity Delivers: by PHT. For each trial, a complete archive of all study source data for • Attributable, legible, contemporaneous, original and accurate (ALCOA) each participating site is checked for quality, integrity, confirmation of patient data that is complete and time-stamped through the use of delivery, and storage. At the trial’s conclusion, PHT delivers the Study alarms, branching logic and edit checks; Archive and all supporting documents to the sponsor and sites, per the • Reduced data variance for improved quality of study results contract with the sponsor and subject to FDA, ICH, EMEA, and other in- and reduced number of patients to show efficacy; ternational regulations and guidance. A final set of Trial Success Program • Real time access to diary data between visits for enhanced safety (TSP) criteria is reviewed and evaluated to close any outstanding issues. and compliance monitoring; Comprehensive data collection by PHT supports regulatory agencies • Expert support for adaptive trial designs that take advantage of the in auditing the electronic records for trustworthiness and quality after reliability and currency of interim data; and study closeout. The entire PHT ePRO trial data package includes eSource • Libraries of experience and metrics regarding data including compliance data stored in XML on durable CD- and DVD-ROM media as well as ALL and data variance/standard deviations for specific indications. trial documentation needed to interpret or establish the conditions in place during the trial. PHT prepares and retains a complete study archive to support reconstruction of a trial, including the records for sites that might lose their archive of the trial records for that site. PHT SitePad Tablet Archived records enable reconstruction of studies. HIPAA suggests The mobile that audit trails record every access (including read-only access) to touch-screen patient information, and not be limited to those actions that change the PC tablet for ePRO collected data. As with data security adherence, PHT is compliant with all archival at sites requirements of Regulations and Guidance in the US, Japan and the Eu- ropean Union. This will be the topic of next quarter’s Insights Newsletter. PHT Corporation 500 Rutherford Avenue info@phtcorp.com Boston, MA 02129 USA www.phtcorp.com Toll-Free: 877-360-2901 Copyright © 2009 PHT Corporation Rev 7.09.2