Cloud Security Demo
•Download as PPTX, PDF•
0 likes•95 views
Cloud Security Demo
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
How to protect your corporate from advanced attacks

How to protect your corporate from advanced attacks
CCI2018 - Azure Security Center - Stato dell’arte e roadmap

CCI2018 - Azure Security Center - Stato dell’arte e roadmap
#ALSummit: Architecting Security into your AWS Environment

#ALSummit: Architecting Security into your AWS Environment
Security O365 Using AI-based Advanced Threat Protection

Security O365 Using AI-based Advanced Threat Protection
Webcast Series #1: Continuous Security and Compliance Monitoring for Global I...

Webcast Series #1: Continuous Security and Compliance Monitoring for Global I...
CSS17: Houston - Introduction to Security in the Cloud

CSS17: Houston - Introduction to Security in the Cloud
CSS17: Houston - Stories from the Security Operations Center

CSS17: Houston - Stories from the Security Operations Center
Similar to Cloud Security Demo
Similar to Cloud Security Demo (20)
Get Ahead of Cyber Attacks with Microsoft Enterprise Mobility + Security

Get Ahead of Cyber Attacks with Microsoft Enterprise Mobility + Security
Get ahead of cybersecurity with MS Enterprise Mobility + Security 

Get ahead of cybersecurity with MS Enterprise Mobility + Security
Identity-Driven Security with Forsyte I.T. Solutions - Demos and Discovery

Identity-Driven Security with Forsyte I.T. Solutions - Demos and Discovery
Power of the Cloud - Introduction to Microsoft Azure Security

Power of the Cloud - Introduction to Microsoft Azure Security
Debugging and interacting with production applications

Debugging and interacting with production applications
Operational Complexity: The Biggest Security Threat to Your AWS Environment

Operational Complexity: The Biggest Security Threat to Your AWS Environment
Global Azure Bootcamp 2018 - Azure Security Center

Global Azure Bootcamp 2018 - Azure Security Center
Running Regulated Workloads on Azure PaaS services (DogFoodCon 2018)

Running Regulated Workloads on Azure PaaS services (DogFoodCon 2018)
Security and DevOps: Agility and Teamwork - SID315 - re:Invent 2017

Security and DevOps: Agility and Teamwork - SID315 - re:Invent 2017
Power of the cloud - Introduction to azure security

Power of the cloud - Introduction to azure security
AWS Security Best Practices for Effective Threat Detection & Response

AWS Security Best Practices for Effective Threat Detection & Response
Xylos Clients Day - Public cloud and security go hand in hand, if you approac...

Xylos Clients Day - Public cloud and security go hand in hand, if you approac...
How Splunk and AWS Enabled End-to-End Visibility for PagerDuty and Bolstered ...

How Splunk and AWS Enabled End-to-End Visibility for PagerDuty and Bolstered ...
More from Cheah Eng Soon
More from Cheah Eng Soon (20)
Microsoft Threat Protection Automated Incident Response 

Microsoft Threat Protection Automated Incident Response
Microsoft Threat Protection Automated Incident Response Demo

Microsoft Threat Protection Automated Incident Response Demo
Azure Weekend 2020 Build Malaysia Bus Uncle Chatbot

Azure Weekend 2020 Build Malaysia Bus Uncle Chatbot
20 common security vulnerabilities and misconfiguration in Azure

20 common security vulnerabilities and misconfiguration in Azure
3 Steps Integrate Microsoft Graph with Azure Bot Services

3 Steps Integrate Microsoft Graph with Azure Bot Services
Data Science - The Most Profitable Movie Characteristic

Data Science - The Most Profitable Movie Characteristic
Start Building Machine Learning Models Faster Than You Think

Start Building Machine Learning Models Faster Than You Think
Recently uploaded
Recently uploaded (20)
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...

Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...
Transcript: #StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

Transcript: #StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
Swan(sea) Song – personal research during my six years at Swansea ... and bey...

Swan(sea) Song – personal research during my six years at Swansea ... and bey...
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Cloud Security Demo
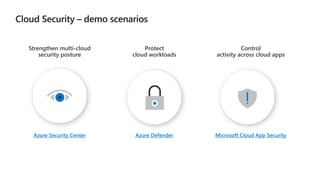
- 1. Azure Security Center Azure Defender Microsoft Cloud App Security Strengthen multi-cloud security posture Protect cloud workloads Control activity across cloud apps
- 2. Azure Security Center Strengthen multi-cloud security posture Azure Security Center Dashboard Multi cloud connectors Secure Score Quick fix recommendations Regulatory compliance Inventory
- 25. Azure Defender Azure Defender Dashboard Vulnerability Assessment Azure Defender for SQL Azure Defender for Storage Azure Defender for Kubernetes Protect cloud workloads
- 57. Discover Cloud apps Protect information from Connected apps Detect anomalous behavior & threats
- 58. Discover Cloud Apps Explore a Snapshot Report Explore Discovered Apps and Risk Scores Sanctioned or Unsanctioned Apps Shadow IT Discovery Report Control activity across cloud apps
- 116. Protect access to connected apps Investigate Connected Apps View a Conditional Access App Control policy Experience Conditional Access App Control in action Control activity across cloud apps
- 210. Detect anomalous user behavior and threats Detect anonymous access Interpret investigation priority score Review Alerts Control activity across cloud apps
