Security Tech: Out With the Old, In With the New [Infographic]
•
6 likes•8,815 views
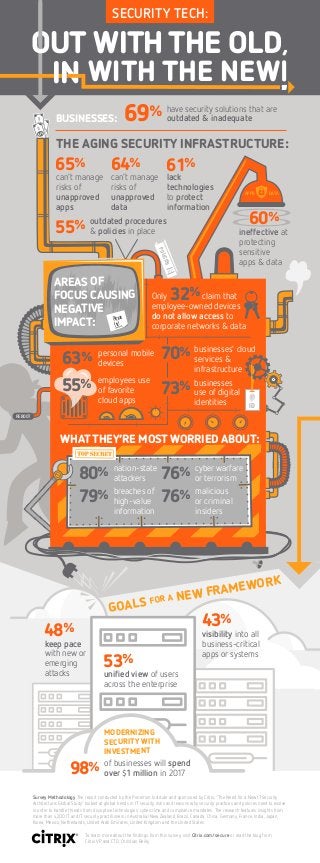
Your outdated security infrastructure is putting your business at risk. A new global security study from Citrix and the Ponemon Institute includes responses from over 4,200 IT professionals from 14 countries. The result? Security professionals are concerned about their security framework and recognize the need for change. Access the full report: http://buff.ly/2iXDPM3
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Viewers also liked (9)
Unified Endpoint Management: Security & Productivity for the Mobile Enterprise

Unified Endpoint Management: Security & Productivity for the Mobile Enterprise
More from Citrix
More from Citrix (20)
Maximize your Investment in Microsoft Office 365 with Citrix Workspace 

Maximize your Investment in Microsoft Office 365 with Citrix Workspace
Deploying Citrix XenApp & XenDesktop Service on Google Cloud Platform

Deploying Citrix XenApp & XenDesktop Service on Google Cloud Platform
Manage Risk by Protecting the Apps and Data That Drive Business Productivity

Manage Risk by Protecting the Apps and Data That Drive Business Productivity
How do Organizations Plan to Assure Application Delivery in a Multi-Cloud World?

How do Organizations Plan to Assure Application Delivery in a Multi-Cloud World?
Workforce Flexibility Can Drive Greater Engagement & Productivity

Workforce Flexibility Can Drive Greater Engagement & Productivity
Citrix Cloud Services: Total Economic Benefits Assessment Guide

Citrix Cloud Services: Total Economic Benefits Assessment Guide
Citrix Cloud Services: Total Economic Benefits Assessment Guide

Citrix Cloud Services: Total Economic Benefits Assessment Guide
Citrix Synergy 2017: Technology Keynote Sketch Notes

Citrix Synergy 2017: Technology Keynote Sketch Notes
Citrix Synergy 2017: Malcolm Gladwell Innovation Super Session Sketch Notes

Citrix Synergy 2017: Malcolm Gladwell Innovation Super Session Sketch Notes
Synergy 2017: Colin Powell Innovation Super Session Sketch Notes

Synergy 2017: Colin Powell Innovation Super Session Sketch Notes
Enterprise Case Study: Enabling a More Mobile Way of Working 

Enterprise Case Study: Enabling a More Mobile Way of Working
Comparing traditional workspaces to digital workspaces

Comparing traditional workspaces to digital workspaces
Recently uploaded
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Recently uploaded (20)
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Security Tech: Out With the Old, In With the New [Infographic]
- 1. REBOOT 69% have security solutions that are outdated & inadequate 65% can’t manage risks of unapproved apps employee-owned devices do not allow access to corporate networks & data Only claim that ineffective at protecting sensitive apps & data 64% can’t manage risks of unapproved data 55% outdated procedures & policies in place 61% lack technologies to protect information APPS DATA 60% 32% personal mobile devices businesses use of digital identities employees use of favorite cloud apps 63% breaches of high-value information 79% malicious or criminal insiders 76% cyber warfare or terrorism 76% nation-state attackers80% 55% businesses’ cloud services & infrastructure 70% GOALS FOR A NEW FRAMEWORK 73% ID 43% visibility into all business-critical apps or systems 53% unified view of users across the enterprise 48% keep pace with new or emerging attacks MODERNIZING SECURITY WITH INVESTMENT 98% of businesses will spend over $1 million in 2017 Survey Methodology The report conducted by the Ponemon Institute and sponsored by Citrix, “The Need for a New IT Security Architecture: Global Study” looked at global trends in IT security risks and reasons why security practices and policies need to evolve in order to handle threats from disruptive technologies, cybercrime and compliance mandates. The research features insights from more than 4,200 IT and IT security practitioners in Australia/New Zealand, Brazil, Canada, China, Germany, France, India, Japan, Korea, Mexico, Netherlands, United Arab Emirates, United Kingdom and the United States. To learn more about the findings from this survey, visit Citrix.com/secure or read the blog from Citrix VP and CTO, Christian Reilly. POLICIES VOL 1 AREAS OF FOCUS CAUSING NEGATIVE IMPACT: Please fix! BUSINESSES: THE AGING SECURITY INFRASTRUCTURE: OUT WITHTHE OLD, IN WITH THE NEW SECURITY TECH: 60% WHAT THEY’RE MOST WORRIED ABOUT:
