2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
•
5 likes•3,600 views
Check Point Software Technologies Ltd. - 2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (20)
Guide scada and_industrial_control_systems_security

Guide scada and_industrial_control_systems_security
NTXISSACSC2 - Securing Industrial Control Systems by Kevin Wheeler

NTXISSACSC2 - Securing Industrial Control Systems by Kevin Wheeler
ICS (Industrial Control System) Cybersecurity Training

ICS (Industrial Control System) Cybersecurity Training
Industrial Control Security USA Sacramento California Oct 13/14

Industrial Control Security USA Sacramento California Oct 13/14
DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 comp...

DTS Solution - Crypto Flow Segmentation addressing NESA IAF and ISO27001 comp...
Using Cyber-Vulnerability Assessment (CVA) to Optimize Control System Upgrade...

Using Cyber-Vulnerability Assessment (CVA) to Optimize Control System Upgrade...
Recent Cybersecurity Concerns and How to Protect SCADA/HMI Applications Prese...

Recent Cybersecurity Concerns and How to Protect SCADA/HMI Applications Prese...
Viewers also liked
Viewers also liked (20)
Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges...

Dubai Cyber Security 01 Ics Scada Cyber Security Solutions and Challenges...
Cyber Security Threats to Industrial Control Systems

Cyber Security Threats to Industrial Control Systems
French acreditation process homologation 2010-01-19

French acreditation process homologation 2010-01-19
Cybersecurity Guide for the State of Washington Critical Infrastructure_9_2015

Cybersecurity Guide for the State of Washington Critical Infrastructure_9_2015
ISACA - China Cybersecurity Law Presentation - Kyle Lai - v3.2

ISACA - China Cybersecurity Law Presentation - Kyle Lai - v3.2
Hacking Critical Infrastructure Like You’re Not a N00b

Hacking Critical Infrastructure Like You’re Not a N00b
Cybersecurity: Critical Infrastructure Threats from Main Street to Wall Street

Cybersecurity: Critical Infrastructure Threats from Main Street to Wall Street
VIVA LA COMPLEJIDAD ! BIG DATA Y TECNOLOGÍA : ELEFANTES EN CIUDADES DE PORCE...

VIVA LA COMPLEJIDAD ! BIG DATA Y TECNOLOGÍA : ELEFANTES EN CIUDADES DE PORCE...
Evaluating System-Level Cyber Security vs. ANSI/ISA-62443-3-3

Evaluating System-Level Cyber Security vs. ANSI/ISA-62443-3-3
Critical Infrastructure and Cybersecurity Transportation Sector

Critical Infrastructure and Cybersecurity Transportation Sector
Industrial Cybersecurity and Critical Infrastructure Protection in Europe

Industrial Cybersecurity and Critical Infrastructure Protection in Europe
Symantec 2010 Critical Infrastructure Protection Study

Symantec 2010 Critical Infrastructure Protection Study
Similar to 2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
Similar to 2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats (20)
Reveelium Smart Predictive Analytics - Datasheet EN

Reveelium Smart Predictive Analytics - Datasheet EN
3.8 Ways to Establish Secure Protocols in a Digital Organization.pdf

3.8 Ways to Establish Secure Protocols in a Digital Organization.pdf
12 IoT Cyber Security Threats to Avoid - CyberHive.pdf

12 IoT Cyber Security Threats to Avoid - CyberHive.pdf
Riordan Network VulnerabilitiesVulnerabilityThreatProbabil.docx

Riordan Network VulnerabilitiesVulnerabilityThreatProbabil.docx
Recently uploaded
Recently uploaded (20)
Dev Dives: Streamline document processing with UiPath Studio Web

Dev Dives: Streamline document processing with UiPath Studio Web
TeamStation AI System Report LATAM IT Salaries 2024

TeamStation AI System Report LATAM IT Salaries 2024
Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Streamlining Python Development: A Guide to a Modern Project Setup

Streamlining Python Development: A Guide to a Modern Project Setup
Nell’iperspazio con Rocket: il Framework Web di Rust!

Nell’iperspazio con Rocket: il Framework Web di Rust!
Gen AI in Business - Global Trends Report 2024.pdf

Gen AI in Business - Global Trends Report 2024.pdf
Unraveling Multimodality with Large Language Models.pdf

Unraveling Multimodality with Large Language Models.pdf
Scanning the Internet for External Cloud Exposures via SSL Certs

Scanning the Internet for External Cloud Exposures via SSL Certs
What's New in Teams Calling, Meetings and Devices March 2024

What's New in Teams Calling, Meetings and Devices March 2024
Unleash Your Potential - Namagunga Girls Coding Club

Unleash Your Potential - Namagunga Girls Coding Club
TrustArc Webinar - How to Build Consumer Trust Through Data Privacy

TrustArc Webinar - How to Build Consumer Trust Through Data Privacy
Leverage Zilliz Serverless - Up to 50X Saving for Your Vector Storage Cost

Leverage Zilliz Serverless - Up to 50X Saving for Your Vector Storage Cost
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
Hyperautomation and AI/ML: A Strategy for Digital Transformation Success.pdf

Hyperautomation and AI/ML: A Strategy for Digital Transformation Success.pdf
DSPy a system for AI to Write Prompts and Do Fine Tuning

DSPy a system for AI to Write Prompts and Do Fine Tuning
2016 Top 10 Critical Infrastructures and SCADA/ICS Cyber Security Vulnerabilities & Threats
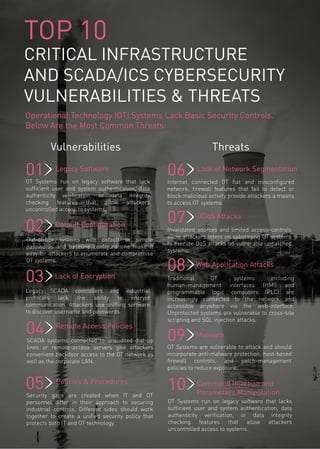
- 1. TOP 10 CRITICAL INFRASTRUCTURE AND SCADA/ICS CYBERSECURITY VULNERABILITIES & THREATS Operational Technology (OT) Systems Lack Basic Security Controls. Below Are the Most Common Threats: OT Systems are vulnerable to attack and should incorporate anti-malware protection, host-based firewall controls, and patch-management policies to reduce exposure. OT Systems run on legacy software that lack sufficient user and system authentication, data authenticity verification, or data integrity checking features that allow attackers uncontrolled access to systems. Legacy Software 01 02 DDoS Attacks Invalidated sources and limited access-controls allow attackers intent on sabotaging OT systems to execute DoS attacks on vulnerable unpatched systems. 03 Malware04 05 Lack of Encryption Legacy SCADA controllers and industrial protocols lack the ability to encrypt communication. Attackers use sniffing software to discover username and passwords. Lack of Network Segmentation 06Internet connected OT flat and misconfigured network, firewall features that fail to detect or block malicious activity provide attackers a means to access OT systems. 07 Policies & Procedures Security gaps are created when IT and OT personnel differ in their approach to securing industrial controls. Different sides should work together to create a unified security policy that protects both IT and OT technology. 08 Web Application Attacks Traditional OT systems including human-management interfaces (HMI) and programmable logic computers (PLC) are increasingly connected to the network and accessible anywhere via the web-interface. Unprotected systems are vulnerable to cross-site scripting and SQL injection attacks. 09 Remote Access Policies SCADA systems connected to unaudited dial-up lines or remote-access servers give attackers convenient backdoor access to the OT network as well as the corporate LAN. 10 Default Configuration Out-of-box systems with default or simple passwords and baseline configurations make it easy for attackers to enumerate and compromise OT systems. Vulnerabilities Threats OT Systems run on legacy software that lacks sufficient user and system authentication, data authenticity verification, or data integrity checking features that allow attackers uncontrolled access to systems. Command Injection and Parameters Manipulation
- 2. ©2016 Check Point Software Technologies Ltd. All rights reserved. January 2016 CONTACT US Worldwide Headquarters | 5 Ha’Solelim Street, Tel Aviv 67897, Israel | Tel: 972-3-753-4555 | Fax: 972-3-624-1100 | Email: info@checkpoint.com U.S. Headquarters | 959 Skyway Road, Suite 300, San Carlos, CA 94070 | Tel: 800-429-4391; 650-628-2000 | Fax: 650-654-4233 | www.checkpoint.com Industrial Control Systems (ICS) used in critical infrastructure and manufacturing industries are targets of sophisticated cyberattacks. The Check Point 1200R rugged appliance line delivers proven, integrated security for deployment in harsh environments as part of a complete end-to-end ICS security solution. WE SECURE THE FUTURE To learn more about Check Point’s Solutions for Critical Infrastructure, please visit www.checkpoint.com/products/industrial-control-systems-appliances
