Grant 2011.0918
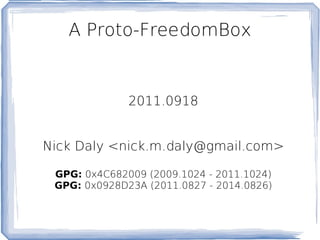
- 1. A Proto-FreedomBox 2011.0918 Nick Daly <nick.m.daly@gmail.com> GPG: 0x4C682009 (2009.1024 - 2011.1024) GPG: 0x0928D23A (2011.0827 - 2014.0826)
- 3. Not how most people use it.
- 5. Facebook (FacebookChat, Skype)
- 10. Other stuff?
- 12. Nothing more than a number, the ultimate captive audience.
- 13. At risk of torture, for your private thoughts.
- 14. Categorized in over 400 ways , including: household income range, age range,political leaning, and gender and age of children in the household, as well as interests in topics including religion, the Bible, gambling, tobacco, adult entertainment and "get rich quick" offers.
- 15. The list goes on.
- 18. Blog Server
- 19. Email Server
- 25. They already use more advanced, secure systems and networks.
- 26. People, not technological faults, bring down these networks.
- 29. Publicizing with a self-evident running example.
- 30. Keeping project momentum high.
- 32. By 10/2: Publish it.
- 34. Get on the mailing list!
- 35. Use privacy and freedom respecting services until the FreedomBox is ready!
- 36. References All the links above :)
Editor's Notes
- Eben proposed the FreedomBox project in February of last year, and it's been a rallying point ever since. A few projects have sprung up, while others gained more followers: - Diaspora (Facebook) - Gnu MediaGoblin (Flickr) - Gnu Social (Twitter) - Identi.ca (Twitter)
- I giggle a little at this slide every time I look at it. &quot;Stolen identifying information&quot; - how can you steal what's sold to almost anyone for practically nothing? But then again, this slide only considers third-party search advertisers. There's still a whole category of folks willing to provide other services to you for nothing more than the cost of your data: online bill pay, E-wallets, etc. Every time you use one of these services, you're saying two things: - I trust that you'll not use my information for purposes I don't intend. - I trust that you'll do a good enough job of keeping my information out of anybody else's hands. Both of these statements are based on trust and you probably have no leverage enforce to either.
- How is the Freedombox supposed to work? - The user unpacks it and plugs it into the wall. - The FBX joins (or creates) your wireless network. - Type in the addresses of your friends and relatives. - Enjoy private and secured communication. - The idea is near zero-configuration for any services involved. - Share your creations (home movies, photos, etc) with virtually no effort.
- “ Security” is a complicated subject based off of a “threat model” - what you're prepared to defend against. It's very situation-specific. The FBX is built with a very different threat model than what those folks need. Without getting into security theory or lots of examples, I'll just say ineffective. You can think of it like this: the average house does a fairly good job of keeping out racoons. You'd need to build a very different house to keep out raptors or the Incredible Hulk. This is designed to run on plug-servers. These servers simply aren't powerful enough to meet their needs. They need a lot of computing power to stay in the dark. It's important to note that this project doesn't bring these folks any new tools they don't already have. Aside from BitTorrent and Anonymous's DDOS attacks, it's been more than 5 years since I've seen evidence of illegal activities brought down by technological failures. Lately, the breaking up of organized criminal rings of things is always credited to someone in the group turning over incriminating information to authorities.
- I also need to get this officially accepted by the FBX community and technical leads. I started on August 2 nd (the day after my first S67 meeting) and plan to finish by October 2 nd . There's still a fair amount that needs to be done: - Config files need to be vetted by relevant communities, telling me whether I've done anything stupid. I was hung up for a week or two on the most difficult configuration question, which I answered yesterday.