Privileged Identity Management: Detect And Prevent Insider Threats
•
0 likes•1,084 views
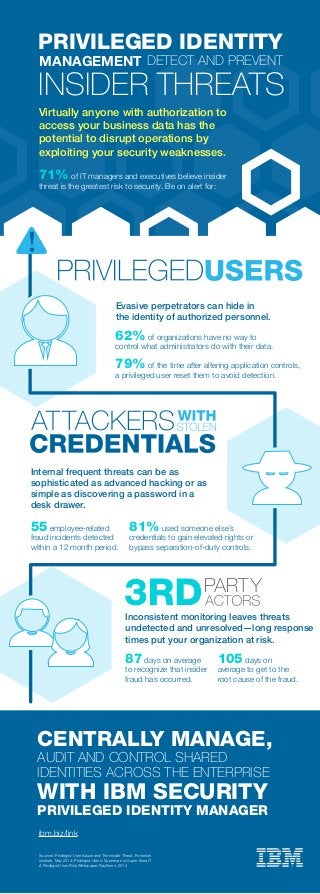
Virtually anyone with authorization to access your business data has the potential to disrupt operations by exploiting your security weaknesses. Read this infographic to learn more:
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
Viewers also liked
Viewers also liked (8)
More from IBM Security
More from IBM Security (20)
Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...

Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...
Bridging the Gap between Privacy and Security: Using Technology to Manage Com...

Bridging the Gap between Privacy and Security: Using Technology to Manage Com...
The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...

The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...
Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...

Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...
Accelerating SOC Transformation with IBM Resilient and Carbon Black

Accelerating SOC Transformation with IBM Resilient and Carbon Black
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
Orchestrate Your Security Defenses; Protect Against Insider Threats 

Orchestrate Your Security Defenses; Protect Against Insider Threats
Recently uploaded
Recently uploaded (20)
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
Privileged Identity Management: Detect And Prevent Insider Threats
- 1. 55 employee-related fraud incidents detected within a 12 month period. 81% used someone else’s credentials to gain elevated rights or bypass separation-of-duty controls. Virtually anyone with authorization to access your business data has the potential to disrupt operations by exploiting your security weaknesses. Evasive perpetrators can hide in the identity of authorized personnel. Internal frequent threats can be as sophisticated as advanced hacking or as simple as discovering a password in a desk drawer. 71% of IT managers and executives believe insider threat is the greatest risk to security. Be on alert for: ibm.biz/link Sources: Privileged User Abuse and The Insider Threat, Ponemon Institute, May 2014; Privileged Users: Superman or Super threat? A Privileged User Risk Whitepaper, Raytheon, 2014 62% of organizations have no way to control what administrators do with their data. 79% of the time after altering application controls, a privileged user reset them to avoid detection. 87 days on average to recognize that insider fraud has occurred. 105 days on average to get to the root cause of the fraud. Inconsistent monitoring leaves threats undetected and unresolved—long response times put your organization at risk. INSIDER THREATS PRIVILEGED IDENTITY MANAGEMENT DETECT AND PREVENT AUDIT AND CONTROL SHARED IDENTITIES ACROSS THE ENTERPRISE CENTRALLY MANAGE, WITH IBM SECURITY PRIVILEGED IDENTITY MANAGER
