Visualizing Security Data with Graph Algorithms
•
4 likes•571 views
This document discusses how security teams are overwhelmed by large volumes of data from security alerts and indicators. It proposes that graph algorithms can help identify related alerts and events that should be investigated together, such as those targeting the same users or part of the same attack. The document provides examples of how community detection, centrality analysis, and other graph algorithms run on preprocessed security data can help prioritize work and generate new threat indicators.
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
AI & ML in Cyber Security - Why Algorithms Are Dangerous

AI & ML in Cyber Security - Why Algorithms Are Dangerous
Graph visualization options and latest developments

Graph visualization options and latest developments
Explain Yourself: Why You Get the Recommendations You Do

Explain Yourself: Why You Get the Recommendations You Do
Finding answers through visualization (GraphDay Barcelona Feb 2016)

Finding answers through visualization (GraphDay Barcelona Feb 2016)
Data Visualization for Big Data: Experience from the Front Line

Data Visualization for Big Data: Experience from the Front Line
Data Science, Personalisation & Product management

Data Science, Personalisation & Product management
Navigating large graphs like a breeze with Linkurious

Navigating large graphs like a breeze with Linkurious
A business level introduction to Artificial Intelligence - Louis Dorard @ PAP...

A business level introduction to Artificial Intelligence - Louis Dorard @ PAP...
Social media monitoring with ML-powered Knowledge Graph

Social media monitoring with ML-powered Knowledge Graph
Improve ml predictions using graph algorithms (webinar july 23_19).pptx

Improve ml predictions using graph algorithms (webinar july 23_19).pptx
Similar to Visualizing Security Data with Graph Algorithms
Similar to Visualizing Security Data with Graph Algorithms (20)
The Pros and Cons of Different Security Detection Technologies.pdf

The Pros and Cons of Different Security Detection Technologies.pdf
Automated Emerging Cyber Threat Identification and Profiling Based on Natural...

Automated Emerging Cyber Threat Identification and Profiling Based on Natural...
C4I cyber secuirty by Eric Eifert - Keynote 9.pptx

C4I cyber secuirty by Eric Eifert - Keynote 9.pptx
AI Cybersecurity: Pros & Cons. AI is reshaping cybersecurity

AI Cybersecurity: Pros & Cons. AI is reshaping cybersecurity
More from Neo4j
More from Neo4j (20)
ISDEFE - GraphSummit Madrid - ARETA: Aviation Real-Time Emissions Token Accre...

ISDEFE - GraphSummit Madrid - ARETA: Aviation Real-Time Emissions Token Accre...
BBVA - GraphSummit Madrid - Caso de éxito en BBVA: Optimizando con grafos

BBVA - GraphSummit Madrid - Caso de éxito en BBVA: Optimizando con grafos
Graph Everywhere - Josep Taruella - Por qué Graph Data Science en tus modelos...

Graph Everywhere - Josep Taruella - Por qué Graph Data Science en tus modelos...
GraphSummit Madrid - Product Vision and Roadmap - Luis Salvador Neo4j

GraphSummit Madrid - Product Vision and Roadmap - Luis Salvador Neo4j
Neo4j_Exploring the Impact of Graph Technology on Financial Services.pdf

Neo4j_Exploring the Impact of Graph Technology on Financial Services.pdf
Rabobank_Exploring the Impact of Graph Technology on Financial Services.pdf

Rabobank_Exploring the Impact of Graph Technology on Financial Services.pdf
Neo4j: Data Engineering for RAG (retrieval augmented generation)

Neo4j: Data Engineering for RAG (retrieval augmented generation)
Neo4j Graph Summit 2024 Workshop - EMEA - Breda_and_Munchen.pdf

Neo4j Graph Summit 2024 Workshop - EMEA - Breda_and_Munchen.pdf
Enabling GenAI Breakthroughs with Knowledge Graphs

Enabling GenAI Breakthroughs with Knowledge Graphs
Neo4j_Anurag Tandon_Product Vision and Roadmap.Benelux.pptx.pdf

Neo4j_Anurag Tandon_Product Vision and Roadmap.Benelux.pptx.pdf
Neo4j Jesus Barrasa The Art of the Possible with Graph

Neo4j Jesus Barrasa The Art of the Possible with Graph
SWIFT: Maintaining Critical Standards in the Financial Services Industry with...

SWIFT: Maintaining Critical Standards in the Financial Services Industry with...
Deloitte & Red Cross: Talk to your data with Knowledge-enriched Generative AI

Deloitte & Red Cross: Talk to your data with Knowledge-enriched Generative AI
Recently uploaded
Recently uploaded (20)
Ensuring Technical Readiness For Copilot in Microsoft 365

Ensuring Technical Readiness For Copilot in Microsoft 365
TeamStation AI System Report LATAM IT Salaries 2024

TeamStation AI System Report LATAM IT Salaries 2024
The Role of FIDO in a Cyber Secure Netherlands: FIDO Paris Seminar.pptx

The Role of FIDO in a Cyber Secure Netherlands: FIDO Paris Seminar.pptx
Streamlining Python Development: A Guide to a Modern Project Setup

Streamlining Python Development: A Guide to a Modern Project Setup
TrustArc Webinar - How to Build Consumer Trust Through Data Privacy

TrustArc Webinar - How to Build Consumer Trust Through Data Privacy
WordPress Websites for Engineers: Elevate Your Brand

WordPress Websites for Engineers: Elevate Your Brand
New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack

"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack
Hyperautomation and AI/ML: A Strategy for Digital Transformation Success.pdf

Hyperautomation and AI/ML: A Strategy for Digital Transformation Success.pdf
Gen AI in Business - Global Trends Report 2024.pdf

Gen AI in Business - Global Trends Report 2024.pdf
What's New in Teams Calling, Meetings and Devices March 2024

What's New in Teams Calling, Meetings and Devices March 2024
DevEX - reference for building teams, processes, and platforms

DevEX - reference for building teams, processes, and platforms
Unleash Your Potential - Namagunga Girls Coding Club

Unleash Your Potential - Namagunga Girls Coding Club
Visualizing Security Data with Graph Algorithms
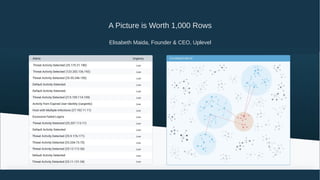
- 1. A Picture is Worth 1,000 Rows Elisabeth Maida, Founder & CEO, Uplevel
- 2. 40 Security Vendors 1,000 Alerts Per Week 3.5 million Indicators Per Month Security teams are overwhelmed with data
- 4. “You need to know what to look for in order to find it” • Can create searches to generate high priority events • Need to know what searches to write • Rules require on-going support and maintenance • Complex queries can be difficult to decode and interpret - “what exactly is this searching for?” • Interactions between overlapping rules can be difficult to untangle
- 6. Graphs can provide a visual indication of activity requiring investigation
- 7. Graph algorithms can help identify events that should be investigated and remediated as a unit - Alerts about the same underlying event generated by different security devices - Sequential events about an ongoing attack - Multiple users targeted using the same tactic or by the same threat actor - Alerts constituting a progressing attack or attack vectors
- 8. Alert Event triggered by a security product identifying potentially malicious behavior Attribute Technical characteristic such as “file hash” Indicator Threat intelligence indicating that a specific attribute (or group of attributes) identifies malicious behavior Terminology
- 9. Community detection algorithms can help identify related alerts Mark Needham and Amy E. Hodler, Graph Algorithms: Practical Examples in Apache Spark and Neo4j
- 11. Pre-processing the graph can enhance the community detection Potential Malware Activity
- 12. Centrality algorithms can help prioritize alert clusters Mark Needham and Amy E. Hodler, Graph Algorithms: Practical Examples in Apache Spark and Neo4j
- 13. FireEye, Double Dragon: APT41, a Dual Espionage and Cyber Crime Operation Output of our pre-processing can also be used to generate new indicators
- 14. Other opportunities for graph algorithms in cybersecurity • Creating attack pattern fingerprints and using graph pattern matching and subgraph isomorphism • Applying label propagation to cascade maliciousness through the graph • Using centrality and betweenness to assess commonality of tactics, techniques, and procedures across attackers
- 15. Thank you!
