Predicate-Preserving Collision-Resistant Hashing
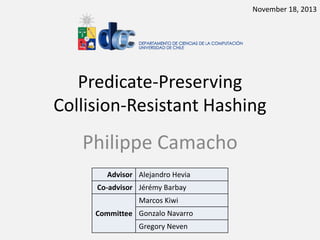
- 1. November 18, 2013 Predicate-Preserving Collision-Resistant Hashing Philippe Camacho Advisor Alejandro Hevia Co-advisor Jérémy Barbay Marcos Kiwi Committee Gonzalo Navarro Gregory Neven
- 4. Motivation How can I be sure that I obtain Bob’s database data and not something else? I need to outsource my database for scaling reasons Bob Cloud Alice We need to handle a short representation of the database. Database
- 5. Collision-Resistance If 𝑋 ≠ 𝑋 ′ and 𝐻 𝑋 = 𝐻 𝑋’ then the adversary has found a collision. 𝑋= openssl.tar.gz V 𝑋′ = File’
- 6. Cryptology = Algorithms ∩ Security This Thesis Computer Science Databases Datastructures Hash Functions Programming Languages Digital Signatures Algorithms Security Operating Systems Networks Distributed Systems Cryptology
- 7. Why Collision-Resistance is not enough 𝑆 = 0111100111111111 How can I convince (efficiently) someone that 𝑺 … contains a 1 in position 5? starts with 0111? contains more 1’s than 0’s ? … 𝑆𝐻𝐴 − 3(𝑆)
- 8. Predicate: P(𝑋, 𝑥) = 𝑇𝑟𝑢𝑒 𝑥 𝜖 𝑋 𝐻(𝑋) 𝑋 = * 𝑥1 , 𝑥2 , 𝑥3 , 𝑥4 , 𝑥5 + 𝐻(𝑋) 𝜋 1 0 3 𝑷𝒓𝒐𝒐𝒇𝑪𝒉𝒆𝒄𝒌 𝐻 𝑋 , 𝑥, 𝜋 = 𝑌𝐸𝑆 𝑥 𝜖 X 𝑷𝒓𝒐𝒐𝒇𝑮𝒆𝒏(𝑋, 𝑥) = 𝜋 2 Known as Accumulators. A lot of applications: e-cash, zero-knowledge sets, anonymous credentials & ring signatures, database authentication, …
- 9. Map Difficult Problem (Still Open BTW) Optimal Data Authentication Accumulators Optimal Data Authentication From Directed Transitive Signatures eprint 4 1 Pivot 6 Strong Accumulators From Collision-Resistant Hashing ISC 2008 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 LatinCrypt 2010 Predicate-Preserving Collision-Resistant Hashing 9 8 2011 Short Transitive Signatures For Directed Trees CT-RSA 2012 Fair Exchange of Short Signatures without CT-RSA Trusted Third Party 2013
- 10. Map Optimal Data Authentication Accumulators 1 Difficult Problem (Still Open BTW) Optimal Data Authentication From Directed Transitive Signatures 4 Pivot 6 Strong Accumulators From Collision-Resistant Hashing 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 Predicate-Preserving Collision-Resistant Hashing 9 8 Short Transitive Signatures For Directed Trees Fair Exchange of Short Signatures without Trusted Third Party
- 11. Outsourcing Securely a Database How can Alice be sure that the reply she gets corresponds to the real state of the database?
- 12. Replay Attack (*) 𝐼𝑁𝑆𝐸𝑅𝑇 (𝑥) 𝑆𝑖𝑔𝑛(𝑆𝐾, 𝑥) = 𝜎 𝑥 𝑌𝐸𝑆: 𝜎 𝑥 Does 𝑥 belong to 𝑋? (*) The reason why trivial solutions don’t work.
- 13. Replay Attack (*) 𝑌𝐸𝑆: 𝜎 𝑥 𝐷𝐸𝐿𝐸𝑇𝐸 (𝑥) Does 𝑥 belong to 𝑋? (*) The reason why trivial solutions don’t work.
- 14. Manager Acc1, Acc2, Acc3 Insert(x) Witness ( x , ) Verify( x , , Acc3) = YES
- 15. Manager Delete(x) Acc1, Acc2, Acc3, Acc4 Alice Verify( x , , Acc4) = NO
- 16. Manager Acc1, Acc2, Acc3 Insert(x) Cryptographic Accumulator Witness ( x , ) Verify( x , , Acc3) = YES
- 17. Manager Acc1, Acc2, Acc3 x1 Alice 1 w1 x2 w2 Alice 2 x3 w3 Alice 3
- 18. Problem: after each update of the accumulated value it is necesarry to recompute all the witnesses.
- 19. Batch Update [FN02] Manager …,Acc99, Acc100, Acc101,…, Acc200,… Upd100,200 Alice 1 (x1,w1,Acc100) ( x2,w2,Acc100) ( x6,w6,Acc100) Alice 2 (x36,w36,Acc100) ( x87,w87,Acc100) Alice 29 Alice 42 (x1,w1,Acc100) ( x20,w20,Acc100) ( x69,w68,Acc100) ( x64,w64,Acc100) (x1,w1,Acc100) ( x2,w2,Acc100) ( x6,w6,Acc100) … ….
- 20. Batch Update [FN02] Manager …,Acc99, Acc100, Acc101,…, Acc200,… Alice 1 (x1,w1’,Acc200) ( x2,w2’,Acc200) ( x6,w6’,Acc200) Alice 2 (x36,w36’,Acc200) ( x87,w87’,Acc200) Alice 29 Alice 42 (x1,w1’,Acc200) ( x20,w20’,Acc200) ( x69,w68’,Acc200) ( x64,w64’,Acc200) (x1,w1’,Acc200) ( x2,w2’,Acc200) ( x6,w6’,Acc200) … ….
- 21. Batch Update [FN02] Trivial solution: 𝑈𝑝𝑑 𝑋 𝑖, 𝑋𝑗 = *list of all witnesses for 𝑋 𝑗+ What we would like: |𝑈𝑝𝑑 𝑋 𝑖, 𝑋𝑗| = 𝑂(1)
- 22. Attack on [WWP08] Manager 𝑿 𝟎 ∶= Ø Insert 𝒙 𝟏 Delete 𝒙 𝟏 Please send 𝑼𝒑𝒅 𝑿 𝟏, 𝑼𝒑𝒅 𝑿 𝟏, 𝑿 𝟏 ∶= *𝒙 𝟏+ 𝑿𝟐 𝑿𝟐 With 𝑼𝒑𝒅 𝑿 𝟏, 𝑿 𝟐 I can update my witness 𝒘 𝒙 𝟏 But 𝒙 𝟏 does not belong to 𝑿 𝟐! 𝑿𝟐 =∅
- 23. Batch Update is Impossible [CH10] • Theorem: Let 𝑨𝒄𝒄 be a secure accumulator scheme with deterministic 𝑼𝒑𝒅𝑾𝒊𝒕 and 𝑽𝒆𝒓𝒊𝒇𝒚 algorithms. For an update involving 𝒎 delete operations in a set of 𝑵 elements, the size of the update information 𝑼𝒑𝒅 𝑿, 𝑿′ required by the algorithm 𝑼𝒑𝒅𝑾𝒊𝒕 is (𝒎 log(𝑵/𝒎)). In particular if 𝒎 = 𝑵/𝟐 we have 𝑼𝒑𝒅 𝑿, 𝑿′ = 𝒎 = (𝑵)
- 24. Map Optimal Data Authentication Accumulators 1 Difficult Problem (Still Open BTW) Optimal Data Authentication From Directed Transitive Signatures 4 Pivot 6 Strong Accumulators From Collision-Resistant Hashing 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 Predicate-Preserving Collision-Resistant Hashing 9 8 Short Transitive Signatures For Directed Trees Fair Exchange of Short Signatures without Trusted Third Party
- 25. What happens when the Database Owner is not Trusted? The adversary is lying! How to prevent such a behaviour? Insert(x) NO OK Belongs(x)
- 26. (New) Security Model [CHKO08] 𝐼𝑛𝑠𝑒𝑟𝑡(𝑥) 𝐼𝑛𝑠𝑒𝑟𝑡(𝑦) Manager Acc1, Acc2, Acc3 Upd1, Upd2, Upd3 𝐷𝑒𝑙𝑒𝑡𝑒(𝑥) 𝑥 ∈ 𝑋? 𝑌𝑒𝑠/𝑁𝑜 𝜋 𝑉𝑒𝑟𝑖𝑓𝑦𝑈𝑝𝑑 𝐴𝑑𝑑 (𝐴𝑐𝑐1 , 𝐴𝑐𝑐2 , 𝑈𝑝𝑑1 ) 𝑉𝑒𝑟𝑖𝑓𝑦 (𝐴𝑐𝑐3 , 𝑥, 𝜋)
- 27. Main Idea of the Construction [CHKO08] • Merkle Trees [M87] P=H(Z1||Z2) Z2=H(Y3||Y4) Z1=H(Y1||Y2) Root value: Represents the set *𝑥1, … , 𝑥8+ Y1=H(x4||x1) x4 x1 Y2=H(x5||x6) x5 x6 Y3=H(x2||x8) x2 x8 Y4=H(x7||x3) x7 x3
- 28. Predicate-Preserving CRHF Proof for predicate 𝒙𝟐 ∈ 𝑿 P=H(Z1||Z2) Z2=H(Y3||Y4) Z1=H(Y1||Y2) H’ 𝑂( log 𝑛) Y1=H(x4||x1) x4 x1 Y2=H(x5||x6) x5 x6 Y3=H(x2||x8) Y4=H(x7||x3) x2 x7 x8 x3
- 29. Technical difficulties • The tree needs to grow dynamically – Not enough to use leaves for storing values • How to handle membership and non-membership predicates – Kocher’s trick [Koch98] • 𝑿 = *𝒙 𝟏 , 𝒙 𝟐 , 𝒙 𝟑 , … , 𝒙 𝒏 + • 𝒙∉ 𝑿⇔ 𝒙𝟐 < 𝒙< 𝒙𝟑 • Some security issues arise – Need to apply padding-techniques (Thanks Gregory!)
- 30. Main Theorem [CHKO08] • Theorem: The accumulator is secure if CRHF exist. All operations run in logarithmic time w.r.t. to the size of the set.
- 31. Map Optimal Data Authentication Accumulators 1 Difficult Problem (Still Open BTW) Optimal Data Authentication From Directed Transitive Signatures 4 Pivot 6 Strong Accumulators From Collision-Resistant Hashing 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 Predicate-Preserving Collision-Resistant Hashing 9 8 Short Transitive Signatures For Directed Trees Fair Exchange of Short Signatures without Trusted Third Party
- 32. A challenging open problem Optimal Data Authentication (ODA) Time to compute the proofs: Time to verify the proof : 𝑂(log 𝑛) 𝑂(1)
- 33. Using (known) accumulators we only get… … 𝑛 = 9, 𝜖 = 1 𝑶( 𝒏) v/s 𝑶(𝟏) 𝑛 = 9, 𝜖 = 2 𝑶( 𝒏) v/s 𝑶(𝟏) 𝜖 = log 𝑛 𝑶(𝐥𝐨𝐠 𝒏) v/s 𝑶(𝐥𝐨𝐠 𝒏) Trade off (Time to compute the proof v/s Time to Verify the proofs) 𝑶(𝝐 𝒏 𝟏/𝝐 ) v/s 𝑶 𝝐
- 34. Intro to Cryptology 0 Map Optimal Data Authentication Accumulators 1 Difficult Problem (Still Open BTW) Optimal Data Authentication From Directed Transitive Signatures 4 Pivot 6 Strong Accumulators From Collision-Resistant Hashing 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 Predicate-Preserving Collision-Resistant Hashing 9 8 Short Transitive Signatures For Directed Trees Fair Exchange of Short Signatures without Trusted Third Party
- 35. How do we sign a graph? Is there a path from 𝑎 to 𝑏? 𝑮 a b
- 36. Trivial Solutions Let 𝒏 = |𝑮|, security parameter 𝛋 When adding a new node… • Sign each edge – Time to sign: 𝑶(𝟏) – Size of signature: 𝑶(𝒏𝜿) bits • Sign each path – Time to sign (new paths): 𝑶(𝒏) – Size of signature: 𝑶(𝜿) bits
- 37. Transitive Signature Schemes [MR02,BN05,SMJ05] Combiner 𝜎 𝑋𝑌 ← 𝑇𝑆𝑖𝑔𝑛(𝑋, 𝑌, 𝜎 𝑋𝑌, ) 𝐴 𝜎 𝐴𝐶 ← 𝐶𝑜𝑚𝑏𝑖𝑛𝑒(𝜎 𝐴𝐵,𝜎 𝐵𝐶 , 𝜎 𝐴𝐵 𝐵 𝜎 𝐴𝐶 ) 𝜎 𝐵𝐶 ← 𝑇𝑉𝑒𝑟𝑖𝑓𝑦(𝐴, 𝐶, 𝜎 𝐴𝐶 , 𝐶 )
- 38. 𝐷𝑇𝑆 ⇒ 𝑂𝐷𝐴 [C11] 𝑡1 𝑡2 𝑡3 𝑶(log 𝒏) 𝑥1 𝑥2 𝑥3 … … 𝑥15 𝑦15 𝑦19 𝑥19 … 𝑥25 𝑥26 𝑥27
- 39. Sounds good, but… • [MR02,BN05,SMJ05] for UNDIRECTED graphs • Transitive Signatures for Directed Graphs (DTS) still OPEN • [Hoh03] DTS ⇒ Trapdoor Groups with Infeasible Inversion
- 40. Intro to Cryptology 0 Map Optimal Data Authentication Accumulators 1 Difficult Problem (Still Open BTW) Optimal Data Authentication From Directed Transitive Signatures 4 Pivot 6 Strong Accumulators From Collision-Resistant Hashing 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 Predicate-Preserving Collision-Resistant Hashing 9 8 Short Transitive Signatures For Directed Trees Fair Exchange of Short Signatures without Trusted Third Party
- 41. Transitive Signatures for Directed Trees
- 42. Previous Work • [Yi07] • Signature size: 𝒏 log(𝒏 log 𝒏) bits • Better than 𝑶(𝒏𝜿) bits for the trivial solution • RSA related assumption • [Neven08] • Signature size: 𝒏 log 𝒏 bits • Standard Digital Signatures 𝑶(𝒏 log 𝒏) bits still impractical
- 43. Our Results • For 𝝐 ≥ 𝟏 𝑶(𝝐) 𝑶(𝝐(𝒏 𝜿)1/𝝐 ) 𝑶(𝝐𝜿) bits • Time to sign edge / verify path signature: • Time to compute a path signature: • Size of path signature: Examples Time to sign edge / verify path signature Time to compute a path signature Size of path signature 𝝐= 𝟏 𝝐= 𝟐 𝝐 = log(𝒏) 𝑶(𝟏) 𝑶(𝟏) 𝑶(log 𝒏) 𝑶(𝒏/𝜿) 𝑶(𝜿) 𝑶( 𝒏/𝜿) 𝑶(𝜿) 𝑶(log 𝒏) 𝑶(𝜿 log 𝒏)
- 44. Pre/Post Order Tree Traversal a b h d i c e f j g Pre order: a b c d e f g h i j k Post order: c e f g d b i j k h a k
- 45. Property of Pre/Post order Traversal • Proposition [Dietz82] There is a path from 𝒙 to 𝒚 𝒑𝒐𝒔 𝒙 < 𝒑𝒐𝒔 𝒚 in 𝑷𝒓𝒆 𝒑𝒐𝒔 𝒚 < 𝒑𝒐𝒔(𝒙) in 𝑷𝒐𝒔𝒕 ⇔ a b h d i c e f j g Pre order: a b c d e f g h i j k Post order: c e f g d b i j k h a k
- 46. Idea Is there a path from 𝑎 to 𝑒? Compute 𝒑𝒐𝒔(𝒙) in 𝑷𝒓𝒆 and 𝑷𝒐𝒔𝒕 E.g.: Sign 𝒂||𝟏||𝟏𝟎 • • Signature of path (𝒂, 𝒆): • Signature of 𝒂||𝟏||𝟏𝟎 • Signature of 𝒆||𝟓||𝟐 a b 𝑮 h d j i c e k • • Check signatures Check 𝟏 < 𝟓 𝟏𝟎 > 𝟐 Challenge: handle changes f Position 1 2 3 4 5 6 7 8 9 10 Pre a b c d e f h i j Post c e f d b i j h a k k Intuition: tricks to assign labels to the vertices so that these labels do not change. We use Order DS. Remaining task: to compare large labels efficiently
- 47. Predicate: P(𝑆, 𝑃) = 𝑇𝑟𝑢𝑒 𝑃 and S share a common prefix 𝐻(𝑆), 𝐻(𝑃) 𝑆 = 1000111 𝑃 = 10000 1 0 2 𝑷𝒓𝒐𝒐𝒇𝑮𝒆𝒏(𝑆, 𝑃) = 𝜋 𝐻 𝑆 , 𝐻(𝑃) 𝜋 3 𝑷𝒓𝒐𝒐𝒇𝑪𝒉𝒆𝒄𝒌 𝐻 𝑆 , 𝐻(𝑃), 𝜋 = 𝑌𝐸𝑆 𝑃 and 𝑆 share a common prefix until position 4 Very easy to derive a bigger family of predicates: • Suffix • Substring • Compare through lexicographical order • …
- 48. Security 𝑯𝑮𝒆𝒏(𝟏 𝜿, 𝒏) → 𝑷𝑲 𝑨𝒅𝒗 𝑨 = 𝐏𝐫 (𝑨, 𝑩, 𝝅, 𝒊) 𝑷𝒓𝒐𝒐𝒇𝑪𝒉𝒆𝒄𝒌 𝑯 𝑨 , 𝑯 𝑩 , 𝒊, 𝝅, 𝑷𝑲 = 𝑻𝒓𝒖𝒆 ∧ 𝑨 𝟏. . 𝒊 ≠ 𝑩 𝟏. . 𝒊
- 49. Bilinear maps (pairings) • 𝑝, 𝑒, 𝐺, 𝐺 𝑇 , 𝑔 ← 𝐵𝑀𝐺𝑒𝑛 1 𝑘 • 𝐺 = 𝐺𝑇 = 𝑝 • 𝑒: 𝐺 × 𝐺 → 𝐺 𝑇 𝑎 𝑏 • 𝑒 𝑔 , 𝑔 = 𝑒 𝑔, 𝑔 • 𝑒 𝑔, 𝑔 generates 𝐺 𝑇 𝑎𝑏 AMAZING TOOL: • Started in 2001 • Thousands of publications • Dedicated Conference (Pairings)
- 50. n-BDHI assumption [BB04] 𝒆: 𝑮 × 𝑮 → 𝑮 𝑻 𝒔 ← 𝒁𝒑 𝒈 generator of𝒏 𝑮 𝟐 𝒔, 𝒈 𝒔 , … , 𝒈 𝒔 ) (𝒈 𝒆(𝒈, 𝒈) 𝟏 𝒔
- 51. The Hash Function • 𝑯𝑮𝒆𝒏(𝟏 𝜿, 𝒏) 𝒑, 𝑮, 𝑮 𝑻, 𝒆, 𝒈 ← 𝐵𝑀𝐺𝑒𝑛 1 𝜅 𝒔 ← 𝒁𝒑 𝟐 𝒏 𝑻: = (𝒈 𝒔 , 𝒈 𝒔 , … , 𝒈 𝒔 ) return 𝑷𝑲: = (𝒑, 𝑮, 𝑮 𝑻, 𝒆, 𝒈, 𝑻) • 𝑯𝑬𝒗𝒂𝒍(𝑴, 𝑷𝑲) 𝒏 𝑯(𝑴) ∶= 𝒈 𝑴 𝒊 𝒔𝒊 𝒊=𝟏 Toy example: 𝑴 = 𝟏𝟎𝟎𝟏 ⇒ 𝑯 𝑴 = 𝒈 𝒔 . 𝒈 𝒔 𝟒
- 52. Generating & Verifying Proofs • 𝑨 = 𝑨 𝟏. . 𝒏 = 𝟏𝟎𝟎𝟎𝟏𝟏𝟏𝟎𝟎𝟏 • 𝑩 = 𝑩,𝟏. . 𝒏- = 𝟏𝟎𝟎𝟎𝟏𝟎𝟏𝟏𝟎𝟎 • 𝜟 ∶= • 𝜟= 𝑯 𝑨 𝑯 𝑩 𝒏 𝒋=𝟏 = 𝒈 𝟓 𝟔 𝟕 𝒈𝒔 𝒈𝒔 𝒈𝒔 𝒈𝒔 𝒈𝒔 𝟓 𝟕 𝟖 𝒈𝒔 𝒈𝒔 𝒈𝒔 𝒈𝒔 𝑪 𝒋 𝒔𝒋 𝟏𝟎 = 𝒈 𝒔 𝟔 𝒈 −𝒔 𝟖 𝒈 𝒔 𝟏𝟎 with 𝑪 = ,𝟎, 𝟎, 𝟎, 𝟎, 𝟎, 𝟏, 𝟎, −𝟏, 𝟎, 𝟏-
- 53. Generating & Verifying Proofs • 𝜟= 𝒏 𝒋=𝟏 𝒈 𝑪 𝒋 𝒔𝒋 with 𝑪 = ,𝟎, 𝟎, 𝟎, 𝟎, 𝟎, 𝟏, 𝟎, −𝟏, 𝟎, 𝟏- • “Remove” factor 𝐬 𝐢+1 in the exponent without knowing 𝐬 𝝅≔ 𝟏 𝜟 𝒔 𝒊+𝟏 𝒏 = 𝒈 𝑪 𝒋 𝒔 𝒋−𝒊−𝟏 = 𝒈 𝒈 𝒋=𝒊+𝟏 • Check the proof : 𝒔 𝒊+1 ) 𝒆(𝝅,𝒈 = 𝒆(𝜟, 𝒈) −𝒔 𝟐 𝒈 𝒔𝟒
- 54. Security [CH12] • Proposition: If the n-BDHI assumption holds, then the previous construction is a CRHF that preserves the common-prefix predicate. • Proof (idea) 𝐀 = 𝟏𝟎𝟎𝟎𝟏𝟎 𝐁 = 𝟏𝟎𝟏𝟎𝟎𝟏 𝐢 = 𝟑 𝐠𝐬 𝐠𝐬 𝟓 𝐇 𝐀 = 𝟑 𝟔 𝐬 𝐠𝐬 𝐠𝐬 𝐇 𝐁 = 𝐠 𝚫 = 𝐇 𝐀 𝐇 𝐁 𝛑 = 𝚫 𝟏 𝒔𝟒 = 𝐠 −𝒔 𝟑 = 𝐠 𝐠 −𝟏 𝒔 𝐬 𝟓 𝐠𝐬 𝒈−𝒔 𝐠 𝟔 −𝐬 𝟐
- 55. Tradeoff 𝒏 = 𝟓𝟒, 𝜿 = 𝟐, 𝒏 𝜿 = 𝟓𝟒 𝟐 = 𝟐𝟕 𝝀 = 𝟑 ⇒ (𝒏 𝜿) 𝟏 𝝀 = 𝟑 𝚺 = 𝒂, 𝒃, 𝒄, 𝒅
- 56. Map Optimal Data Authentication Accumulators 1 Difficult Problem (Still Open BTW) Optimal Data Authentication From Directed Transitive Signatures 4 Pivot 6 Strong Accumulators From Collision-Resistant Hashing 2 Transitive Signatures 5 7 Impossibility of Batch Update For Cryptographic Accumulators 3 Predicate-Preserving Collision-Resistant Hashing 9 8 Short Transitive Signatures For Directed Trees Fair Exchange of Short Signatures without Trusted Third Party
- 57. Modeling Transactions with Digital Signatures The problem: Who starts first? Impossibility Result [Cleve86] Software License Digital Check Buyer Seller
- 58. Gradual Release of a Secret Bob’s signature Alice’s signature 1 1001 0 Allows to circumvent Cleve’s impossibility result 0 (relaxed security definition). 1 0 1 How do I know that the bit I received 1 is not garbage? 1 0111
- 59. Contributions • Formal definition of Partial Fairness • Efficiency 𝜿: Security Parameter # Rounds Communication # Crypto operations per participant 𝜅+5 𝜿 = 𝟏𝟔𝟎 165 16𝜅 2 + 12𝜅 bits ≈ 52 kB ≈ 30𝜅 ≈ 4800 • First protocol for Boneh-Boyen signatures
- 60. I will try to open the box with another value. I will attempt to find out what is in the box before I get the key. Commitments Commitment secret 1 3 2 + secret = secret The secret is revealed.
- 61. Zero-Knowledge Proofs of Knowledge Prove you know the content of the box and something about this content without opening the box. I want to fool Alice: Make her believe that the value in the box is binary while it is not (e.g: 15). 1 I want to know exactly what is in the box (not only that the secret is a bit). 0 , 𝜋 2 0 + 𝜋 = Yes / No
- 62. Intuition of the Construction [C13] 1 Signature + 35 = 100011 2 Encrypted Signature = 2 1 3 𝜋1 Each small box contains a bit. 𝜋2 The sequence of small boxes is the binary decomposition of the secret inside the big box. 4 1 0 0 0 0 0 0 1 1 1 1
- 63. Conclusion • We introduced the concept of Predicate-Preserving Collision-Resistant Hashing • Many open questions – Optimal Data Authentication – Relationship between predicate complexity and size for proofs – Apply these techniques to authenticated pattern matching – Find new applications…
- 64. Bibliography • • • • • • • • [BB04] Dan Boneh and Xavier Boyen. Short Signatures Without Random Oracles. In Christian Cachin and Jan Camenisch, editors, EUROCRYPT 2004. [ BN05] Mihir Bellare and Gregory Neven. Transitive Signatures: New Schemes and Proofs. IEEE Transactions on Information Theory, 51(6):2133–2151, 2005. [ Cleve86] Richard Cleve. Limits on the security of coin flips when half the processors are faulty. In STOC, 1986. [ Dietz82 ] Paul F. Dietz. Maintaining Order in a Linked List. In STOC, pages 122– 127. ACM Press, May 1982. [ FN02] Nelly Fazio and Antonio Nicolisi. Cryptographic Accumulators: Definitions, Constructions and Applications. Technical report, 2002. [GM84] Goldwasser, Shafi, and Silvio Micali. "Probabilistic encryption." Journal of computer and system sciences , 1984 [GMR88] Shafi Goldwasser, Silvio Micali, and Ronald L. Rivest. A Digital Signature Scheme Secure Against Adaptive Chosen-Message Attacks. SIAM, 1988. [ Hoh03] Susan Rae Hohenberger. The Cryptographic Impact of Groups with Infeasible Inversion. Master’s thesis, Massachusetts Institute of Technology, 2003.
- 65. Bibliography • • • [MR02] Silvio Micali and Ronald Rivest. Transitive Signature Schemes. In Bart Preneel, editor, CT-RSA, 2002. [SMJ05] Siamak Fayyaz Shahandashti, Mahmoud Salmasizadeh, and Javad Mohajeri. A Provably Secure Short Transitive Signature Scheme from Bilinear Group Pairs. In Carlo Blundo and Stelvio Cimato, editors, Security in Communication Networks, 2005. [WWP08] Peishun Wang, Huaxiong Wang, and Josef Pieprzyk. Improvement of a Dynamic Accumulator at ICICS 07 and Its Application in Multi-user Keyword-Based Retrieval on Encrypted Data. In Asia-Pacific Conference on Services Computing, 2008.
- 66. Strong Accumulators from CRHF
- 67. Hashing: padding-techniques The trees are different yet yield the same hash value. We need to hash the final value (root) and concatenated with some data on the “shape” of the tree: 𝑯(𝑯’(𝒂||𝒃)||𝟏||𝟏)
- 68. Batch Update
- 69. Batch Update is Impossible [CH10] • Theorem: Let 𝑨𝒄𝒄 be a secure accumulator scheme with deterministic 𝑼𝒑𝒅𝑾𝒊𝒕 and 𝑽𝒆𝒓𝒊𝒇𝒚 algorithms. For an update involving 𝒎 delete operations in a set of 𝑵 elements, the size of the update information 𝑼𝒑𝒅 𝑿, 𝑿′ required by the algorithm 𝑼𝒑𝒅𝑾𝒊𝒕 is (𝒎 log(𝑵/𝒎)). In particular if 𝒎 = 𝑵/𝟐 we have |𝑼𝒑𝒅 𝑿, 𝑿′| = (𝒎) = (𝑵)
- 70. Proof 1/3 Manager User X={x1,x2,…,xN} X={x1,x2,…,xN} AccX , {w1,w2,…,wN} Compute AccX, {w1,w2,…,wN} Delete Xd:={xi1,xi2,…,xim} X’ := XXd AccX’ , UpdX,X’ Compute AccX’,UpdX,X’
- 71. Proof 2/3 CASE 1 User X={x1,x2,…,xN} {w1,…,wN} AccX, AccX’, UpdX,X’ CASE 2 If x is not in X’ => Scheme insecure If x is in X’ => Scheme incorrect x still in X’ x not in X’ anymore YES For each element x xєX w’ := UpdWit(w,AccX,AccX’,UpdX,X’) CASE 1 w’ valid? NO CASE 2 User can reconstruct the set Xd
- 72. Proof 3/3 • There are ( ) subsets of m elements in a set of N elements N m • We need log( to encode Xd N m ) ≥ m log(N/m) bits
- 74. If the 𝑉𝑒𝑟𝑖𝑓𝑦 algorithm returns 𝑌𝐸𝑆, I am sure Alice is the author of message 𝑚. Digital Signatures SK PK PK 𝜎 = 𝑆𝑖𝑔𝑛(𝑆𝐾, 𝑚) 𝑌𝐸𝑆/𝑁𝑂 = 𝑉𝑒𝑟𝑖𝑓𝑦(𝑃𝐾, 𝜎, 𝑚)
- 75. Security for Digital Signatures [GMR88] 𝑃𝐾 Signature request for message 𝑚1 (Adversary) 𝜎1 (Oracle) Signature request for message 𝑚2 𝜎2 … Signature request for message 𝑚 𝑖 𝜎𝑖 This should not happen! (𝜎, 𝑚) such that 𝑉𝑒𝑟𝑖𝑓𝑦(𝑃𝐾, 𝜎, 𝑚) returns 𝑌𝐸𝑆 but 𝑚 has not been requested before
- 76. Security of transitive signatures [MR02] (𝐴, 𝐵) 𝜎 𝐴𝐵 (𝐵, 𝐶) σBC (𝐵, 𝐷) 𝜎 𝐵𝐷 (𝐴, 𝐸) 𝜎 𝐴𝐸 𝐴 𝐵 𝐶 E 𝐷 𝜎 ∗ , 𝐵, 𝐸 : ← 𝑇𝑉𝑒𝑟𝑖𝑓𝑦(𝐵, 𝐸, 𝜎 ∗ , ) and There is no path from 𝑩 to 𝑬
- 77. ODA is still open • [PTT10] Papamanthou, Charalampos, Roberto Tamassia, and Nikos Triandopoulos. "Optimal authenticated data structures with multilinear forms." Pairing-Based CryptographyPairing 2010. Springer Berlin Heidelberg, 2010. 246-264. • [CLT13] Coron, Jean-Sébastien, Tancrede Lepoint, and Mehdi Tibouchi. "Practical Multilinear Maps over the Integers." IACR Cryptology ePrint Archive 2013 (2013): 183. [PTT10] Only works for the two-party model. Size of proof are 𝑶(𝟏) but time to verify is 𝑶 log 𝒏 . [CLT13] We know how to build multilinear maps!
- 78. Fair Exchange
- 79. Partial Fairness 𝑂 𝑆𝑖𝑔𝑛 𝑠𝑘 𝐵 ,⋅ (𝑠𝑘 𝐴 , 𝑝𝑘 𝐴 ) 𝑚 𝐴, 𝑚 𝐵 Not queried to signing oracle 𝑂 𝑆𝑖𝑔𝑛 𝑚 𝐴 , 𝑚 𝐵 , 𝑝𝑘 𝐴 (𝑠𝑘 𝐵 , 𝑝𝑘 𝐵 ) 𝜎 𝐵 on 𝑚 𝐴 σ 𝐴 on 𝑚 𝐵 σ∗ on 𝑚∗ Bet according to partially released secret
- 80. Simultaneous Hardness of Bits for Discrete Logarithm Holds in the generic group model [Schnorr98] An adversary cannot distinguish between a random sequence of 𝜿 − 𝒍 bits and the first 𝜿 − 𝒍 bits of 𝜽 given 𝒈 𝜽 . 𝑙 = 𝜔( log 𝜅)
- 82. Provable Security 1. Define “Secure” (formally) It’s not that easy. E.g. [GM84] 2. Design your solution We want: If conjecture is true then NO adversary can break the security. We prove: If adversary can break the security then the conjecture is false. 3. Prove it is secure with respect to definition proposed in step 1 4. Don’t forget to mention your assumptions (mathematical conjectures) E.g. : Factoring is hard.
- 83. Provable Security 1. Given a random hash function 𝑯 it should be hard for any adversary to find to messages 𝒎, 𝒎’ such that 𝑯(𝒎) = 𝑯(𝒎’) and 𝒎 ≠ 𝒎’ 2. 𝑮 a cyclic group , 𝒈 a generator, 𝜶 a random value set 𝒉: = 𝒈 𝜶 and define for 𝒎 = 𝒎 𝟏 ||𝒎 𝟐 : 𝑯(𝒎 𝟏 | 𝒎 𝟐 ∶= 𝒈 𝒎 𝟏 𝒉 𝒎 𝟐 3. If adversary finds different 𝒎, 𝒎’ such that 𝑯(𝒎) = 𝑯(𝒎’) then we can deduce 𝜶 . 4. Discrete logarithm is hard: given 𝒈, 𝒉 it’s difficult (takes a lot of time) to compute 𝜶 such that 𝒉 = 𝒈 𝜶
